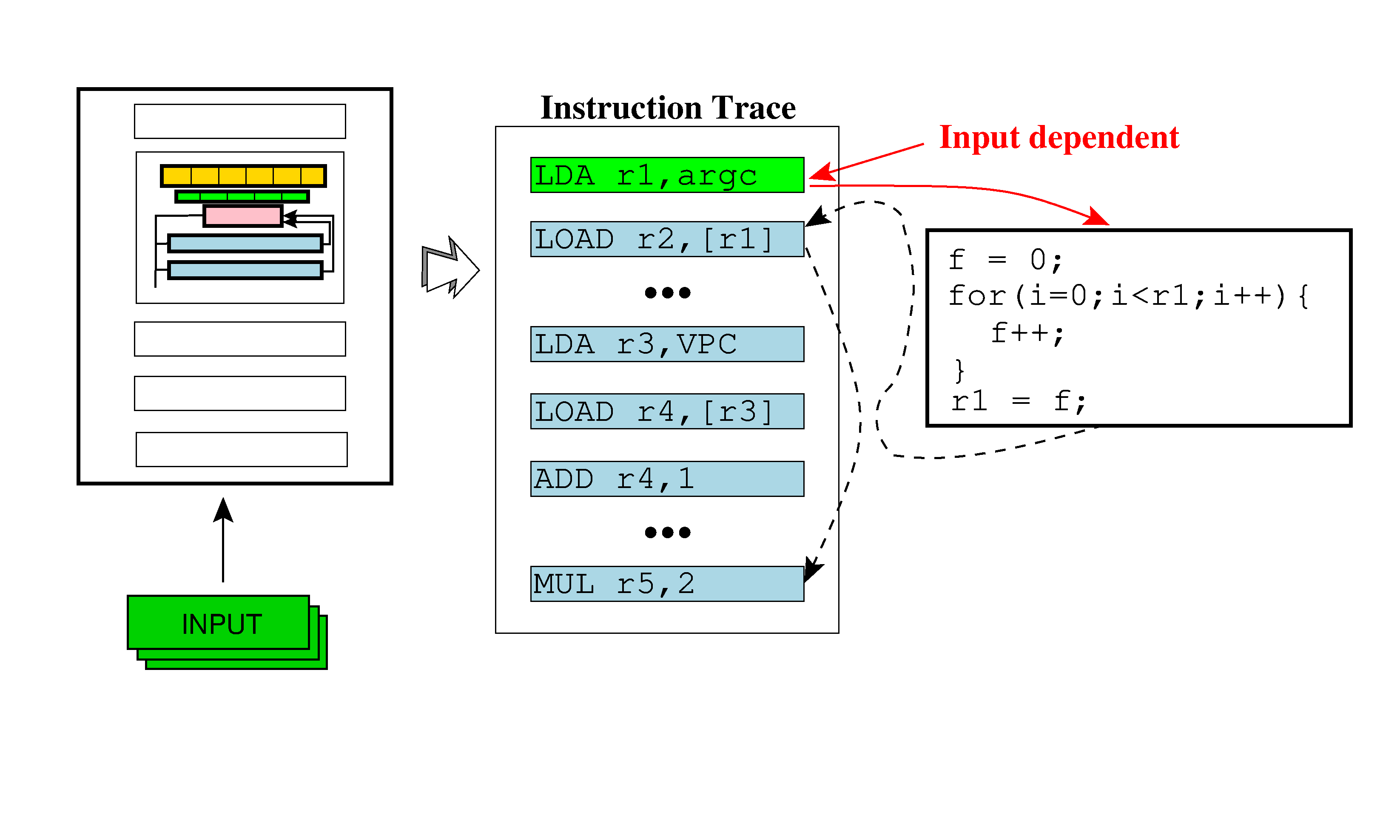
Static program analysis assisted dynamic taint tracking for software vulnerability discovery - ScienceDirect
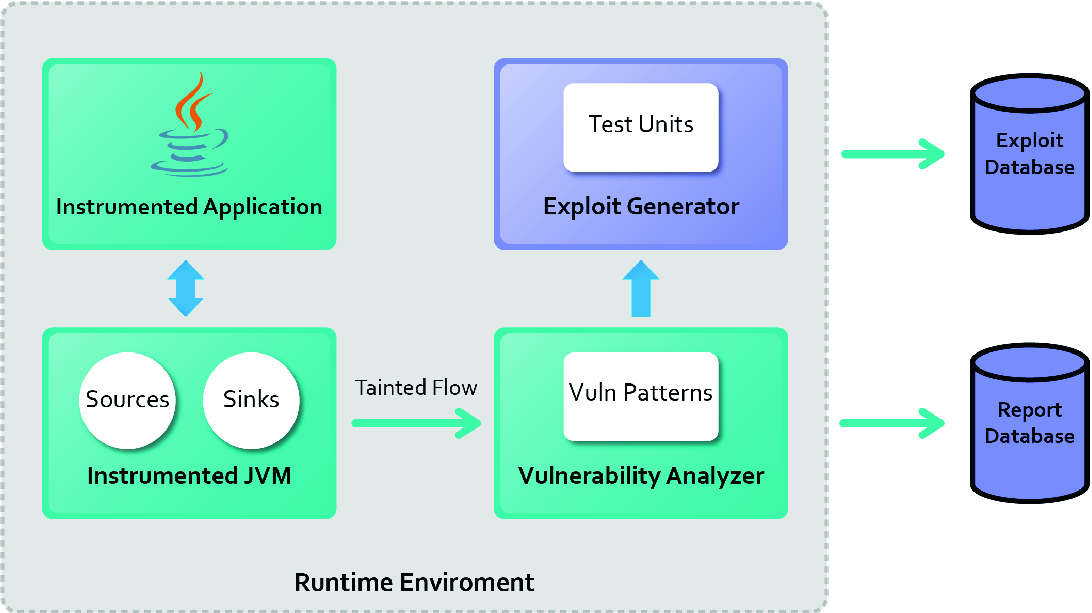
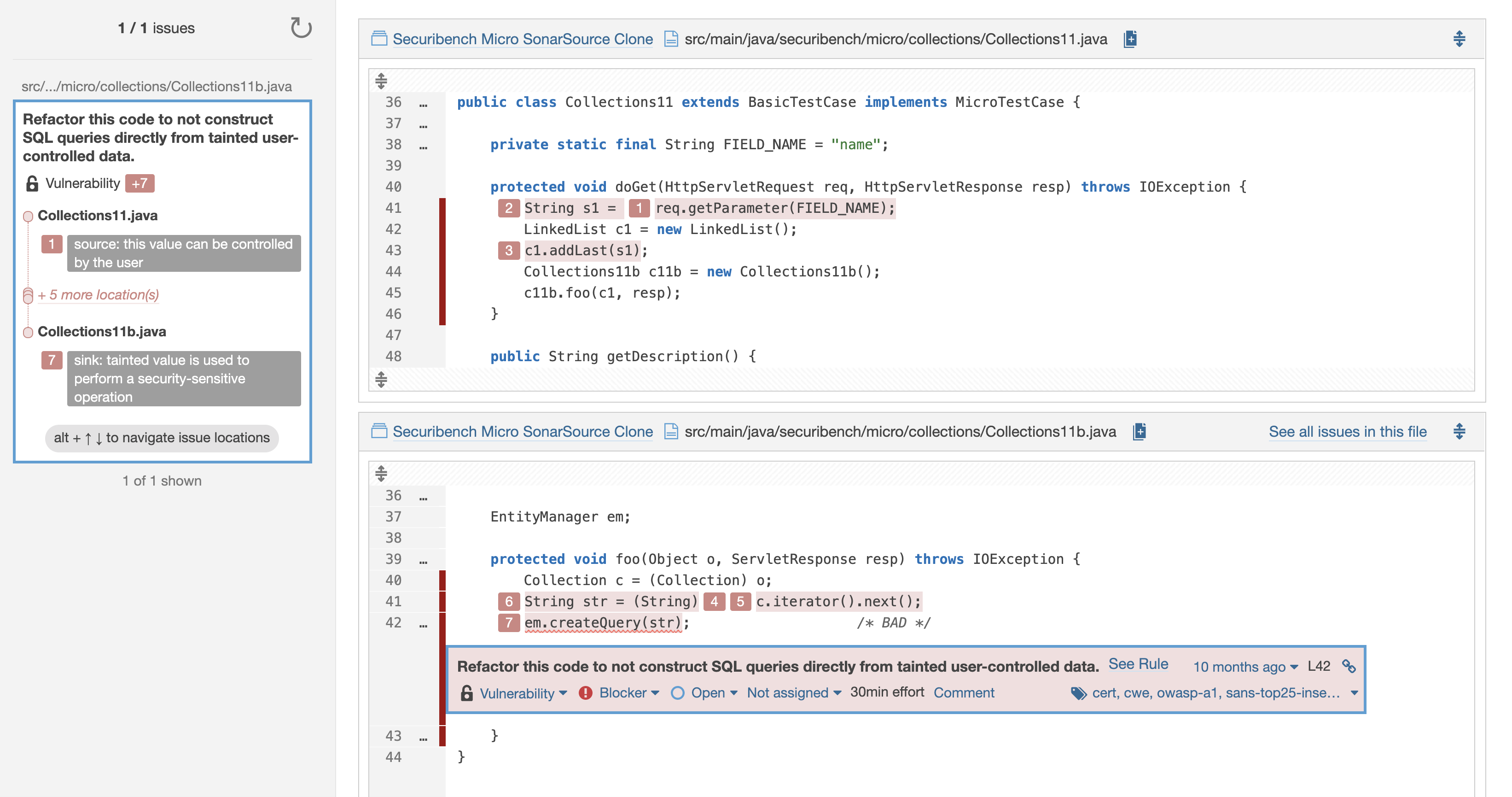
Practical Dynamic Taint Tracking for Exploiting Input Sanitization Error in Java Applications | SpringerLink

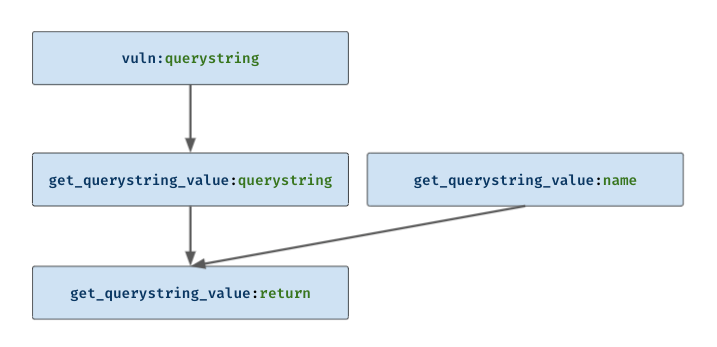
USING TAINT ANALYSIS TO TRACE WHETHER THE MODULE IS CONTAMINATED VIA... | Download Scientific Diagram

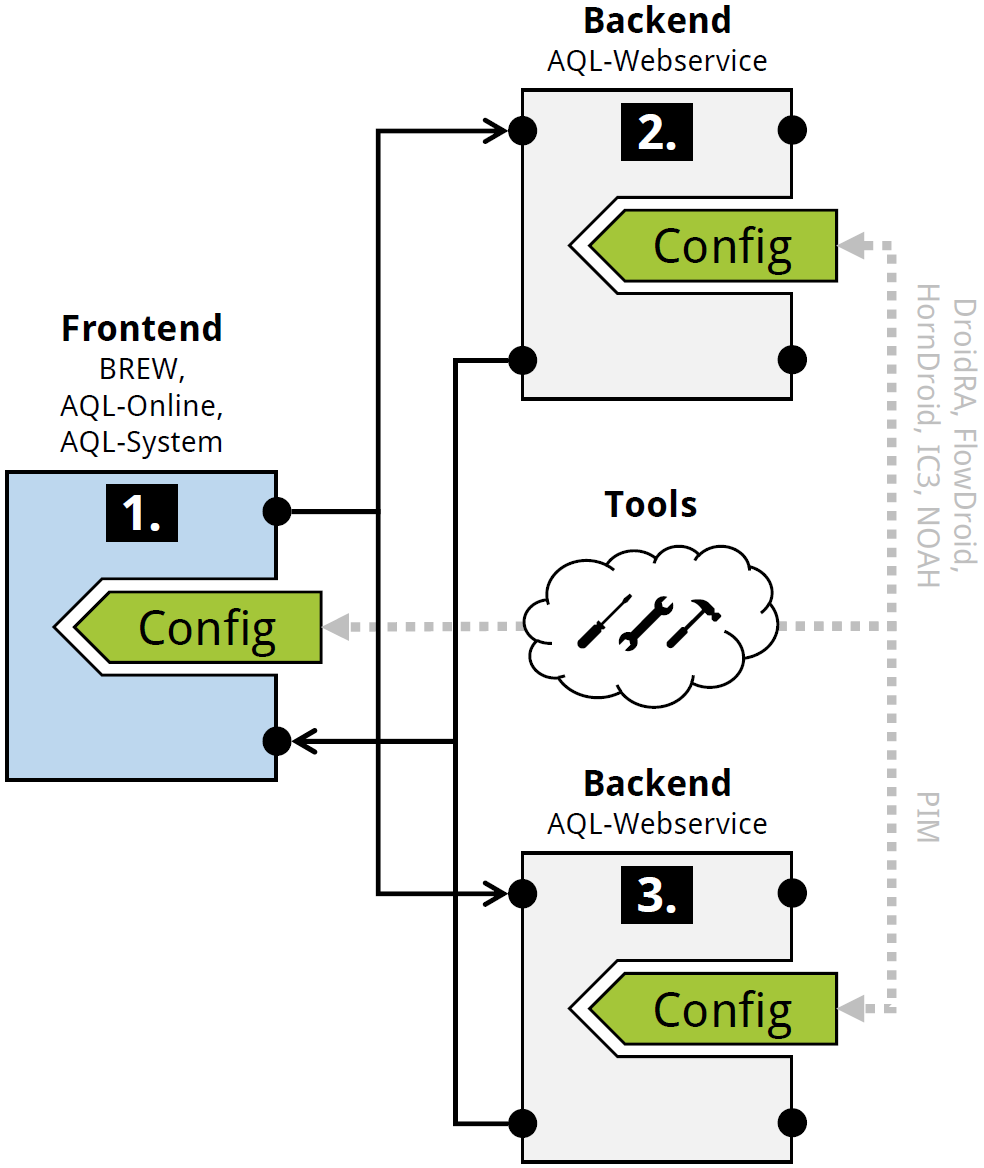
Eric Bodden on Twitter: "All three badges for our #FSE18 reproducibility study on Android taint analysis tools! Yeah! https://t.co/UUssCuXbbm" / Twitter

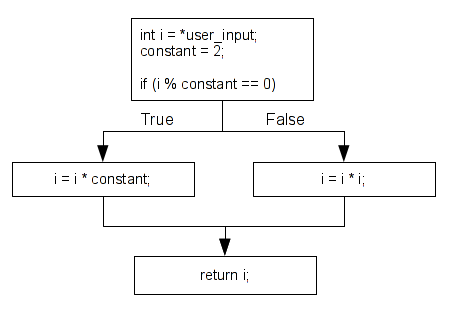
Use of taint analysis to determine whether the module is contaminated... | Download Scientific Diagram

Table 1 from On the effectiveness of dynamic taint analysis for protecting against private information leaks on Android-based devices | Semantic Scholar


![PDF] A Dynamic Taint Analysis Tool for Android App Forensics | Semantic Scholar PDF] A Dynamic Taint Analysis Tool for Android App Forensics | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/7a21e9df6494e10424ddb10cbfde3f83df6ea7bd/6-Figure2-1.png)

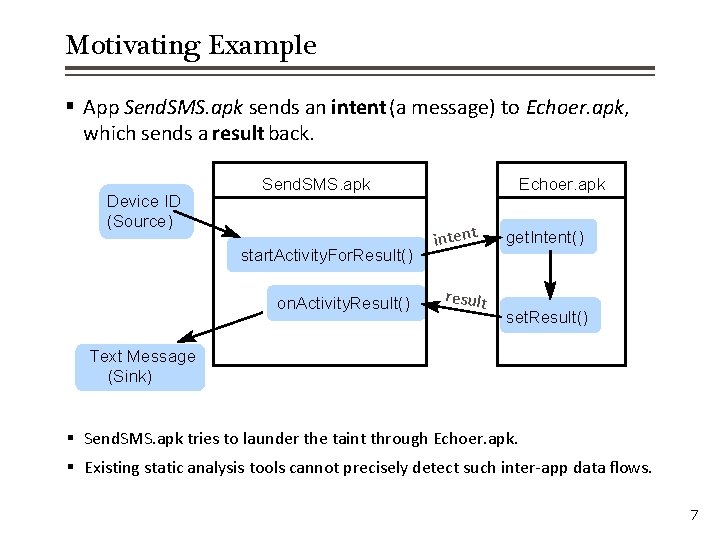
![PDF] Static Taint Analysis Tools to Detect Information Flows | Semantic Scholar PDF] Static Taint Analysis Tools to Detect Information Flows | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/52eedcf97b491873fc9afdf3e33d53fb3578cb52/2-Figure1-1.png)
![equation]: Backward Context-Sensitive Flow Reconstruction of Taint Analysis Results | SpringerLink equation]: Backward Context-Sensitive Flow Reconstruction of Taint Analysis Results | SpringerLink](https://media.springernature.com/original/springer-static/image/chp%3A10.1007%2F978-3-030-39322-9_2/MediaObjects/487236_1_En_2_Fig2_HTML.png)