An efficient authentication and key agreement protocol for IoT-enabled devices in distributed cloud computing architecture | EURASIP Journal on Wireless Communications and Networking | Full Text
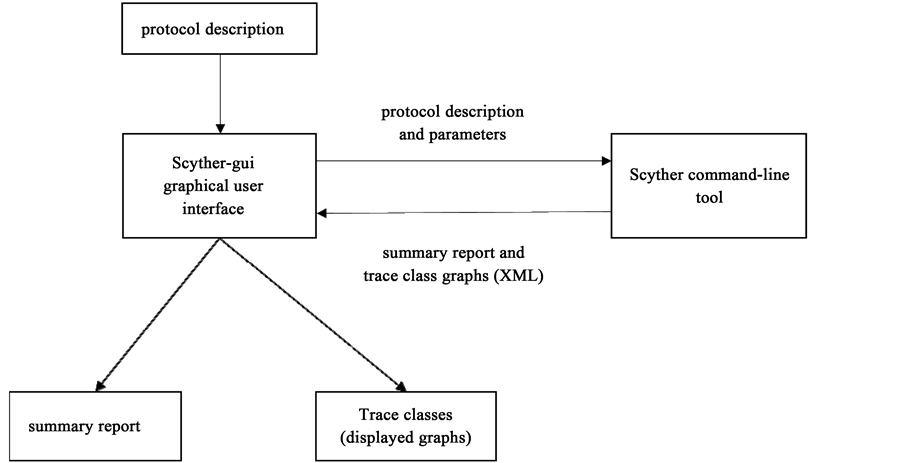
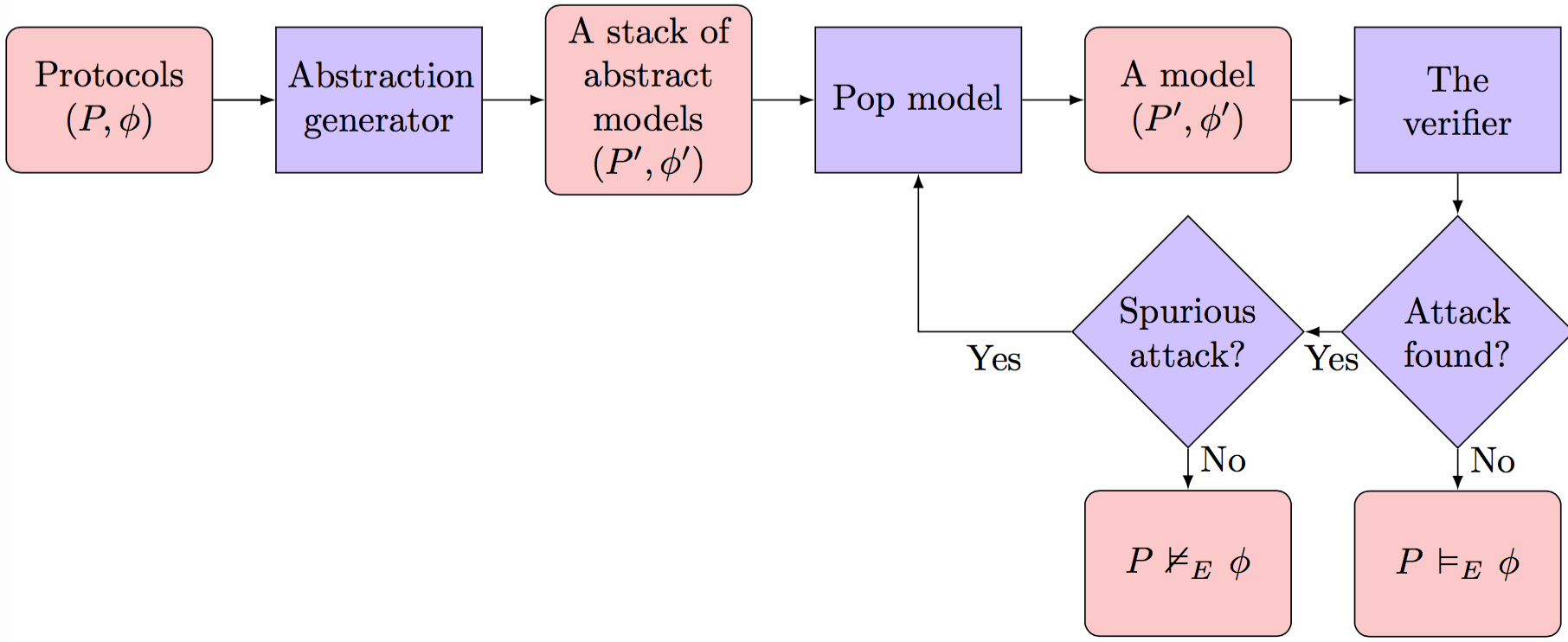
GitHub - binhnguyen1984/scyther-abstraction: The Scyther-abstraction Tool for the symbolic analysis of security protocols
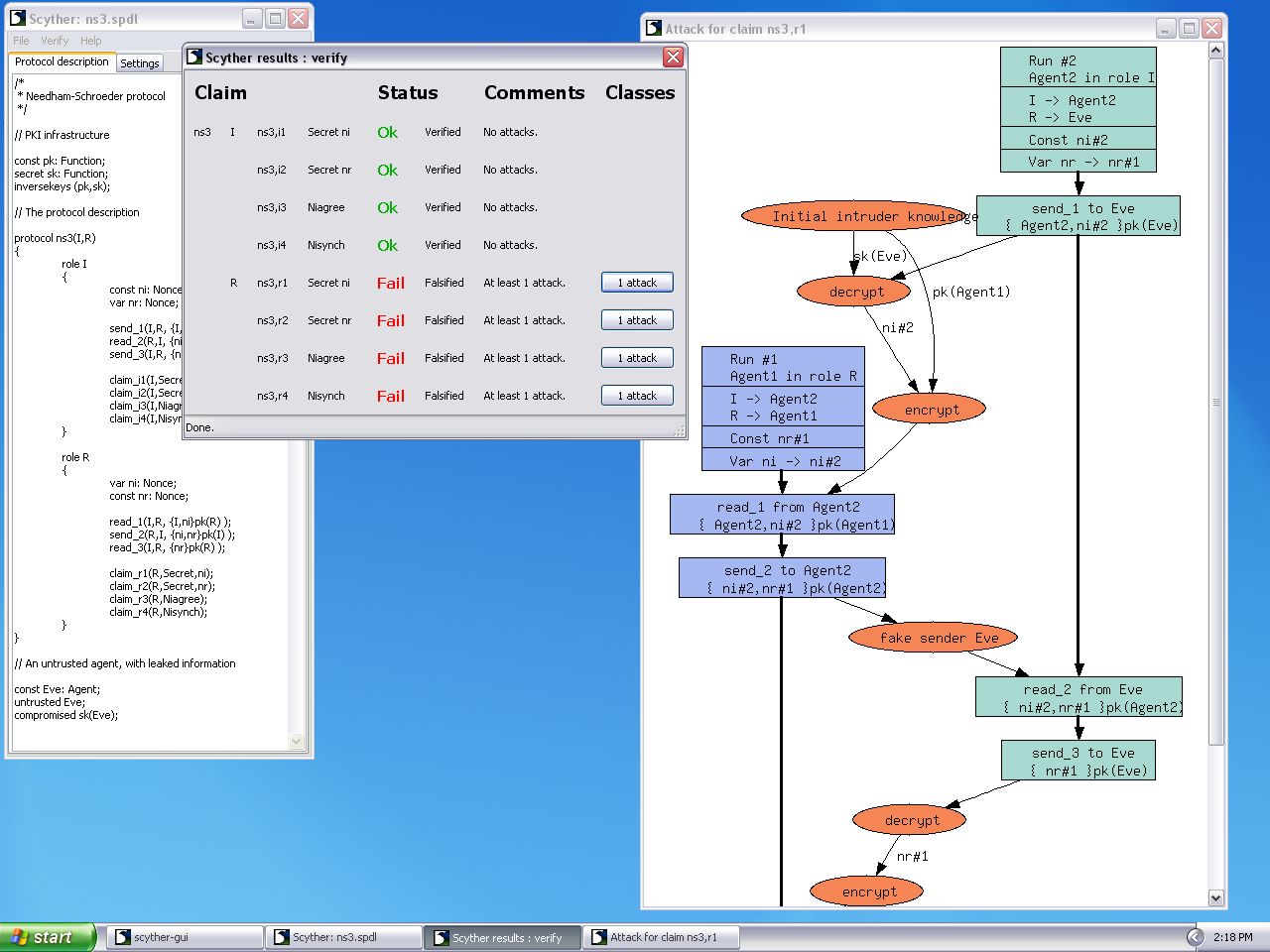
Snapshot of SCYTHER tool: experimenting using various types of attacks | Download Scientific Diagram

Cryptanalysis and improvement of the YAK protocol with formal security proof and security verification via Scyther - Mohammad - 2020 - International Journal of Communication Systems - Wiley Online Library
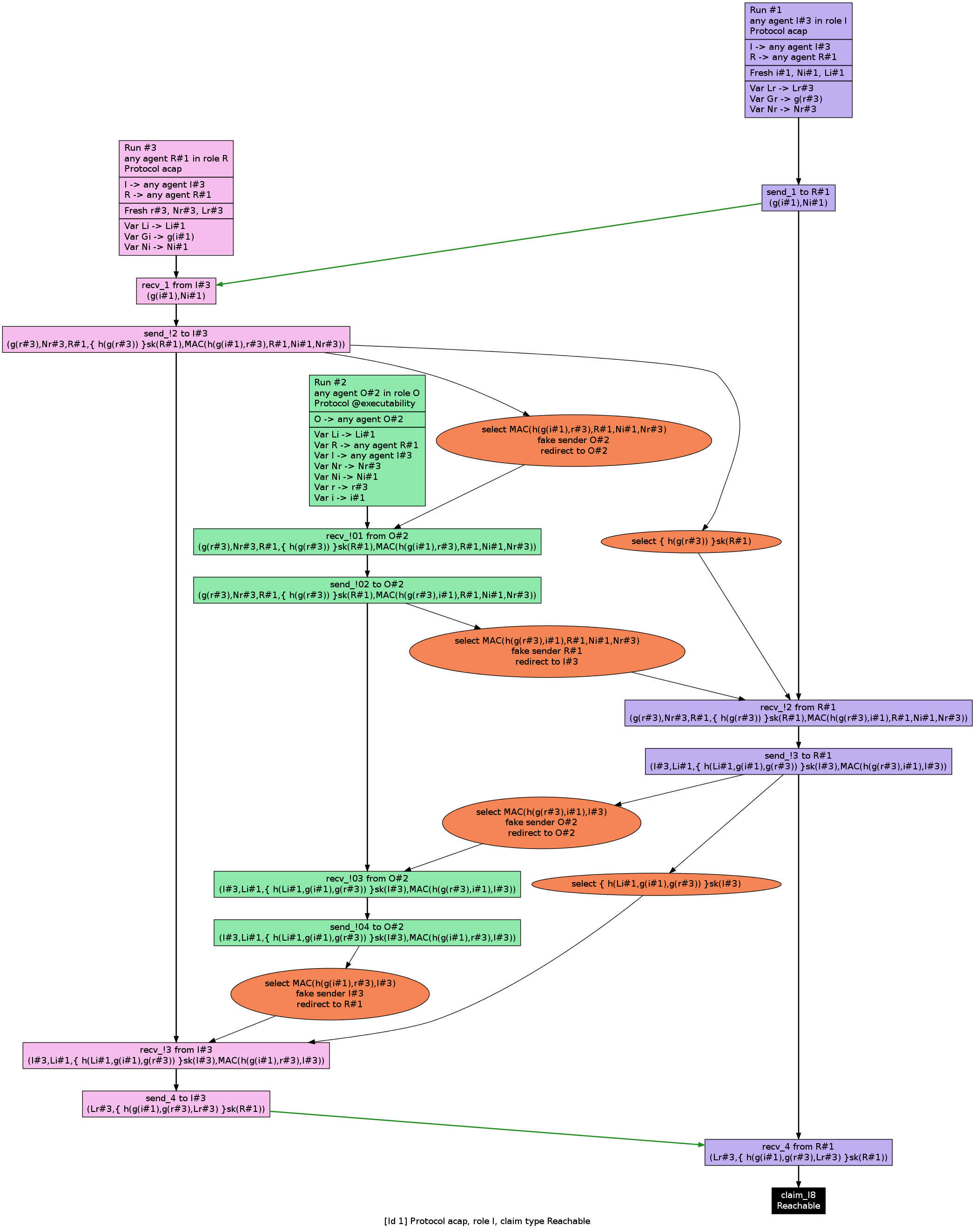
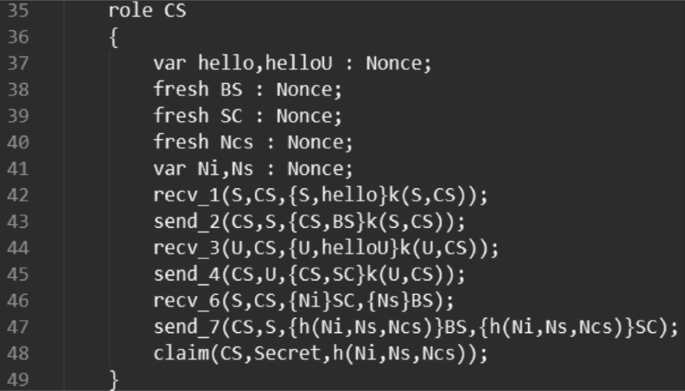
![PDF] Analysis and Verification of a Key Agreement Protocol over Cloud Computing Using Scyther Tool | Semantic Scholar PDF] Analysis and Verification of a Key Agreement Protocol over Cloud Computing Using Scyther Tool | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/df932f9db948e0e49c26a748ca2eec9d76e3c118/6-Figure4-1.png)
PDF] Analysis and Verification of a Key Agreement Protocol over Cloud Computing Using Scyther Tool | Semantic Scholar

An online security protocol for NFC payment: Formally analyzed by the scyther tool | Semantic Scholar